Microsoft 365
This guide walks you through integrating Microsoft Office 365 with Fixiam using SAML-based Single Sign-On (SSO). You'll begin from IAM, configure your domain with Microsoft, and complete user assignment and testing.
Prerequisites
- Admin access to Microsoft 365 and Fixiam
- A verified domain (e.g. yourcompany.com)
- A working PowerShell setup with the MSOnline module
- At least one user in Microsoft 365 and Fixiam with matching email
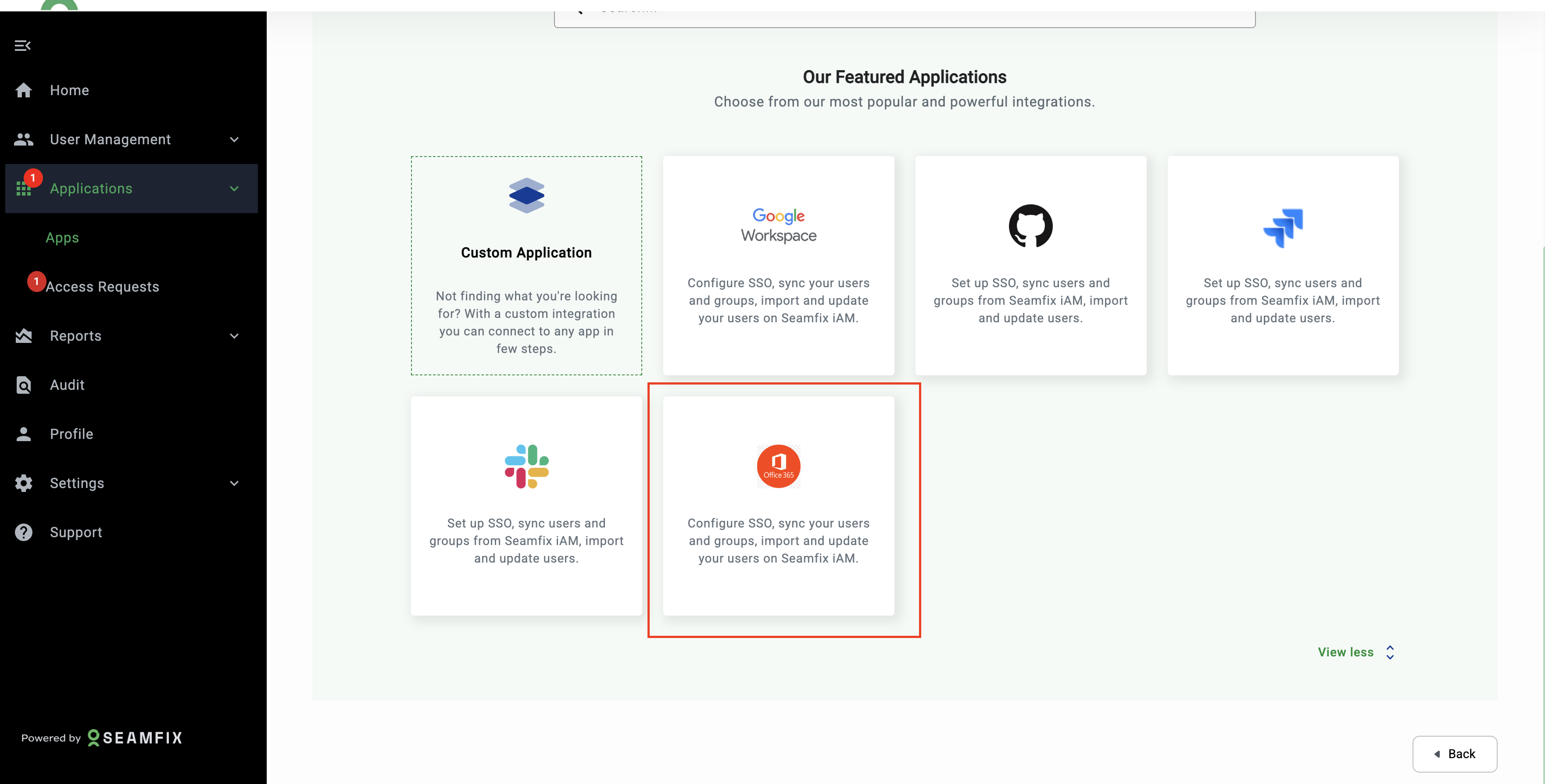
Step 1:Start from Fixiam
- Log in to your Fixiam account: https://iam.seamfix.com
- Go to Applications > Apps
- Click Add New Application
- Select Office 365 from the list of Applications
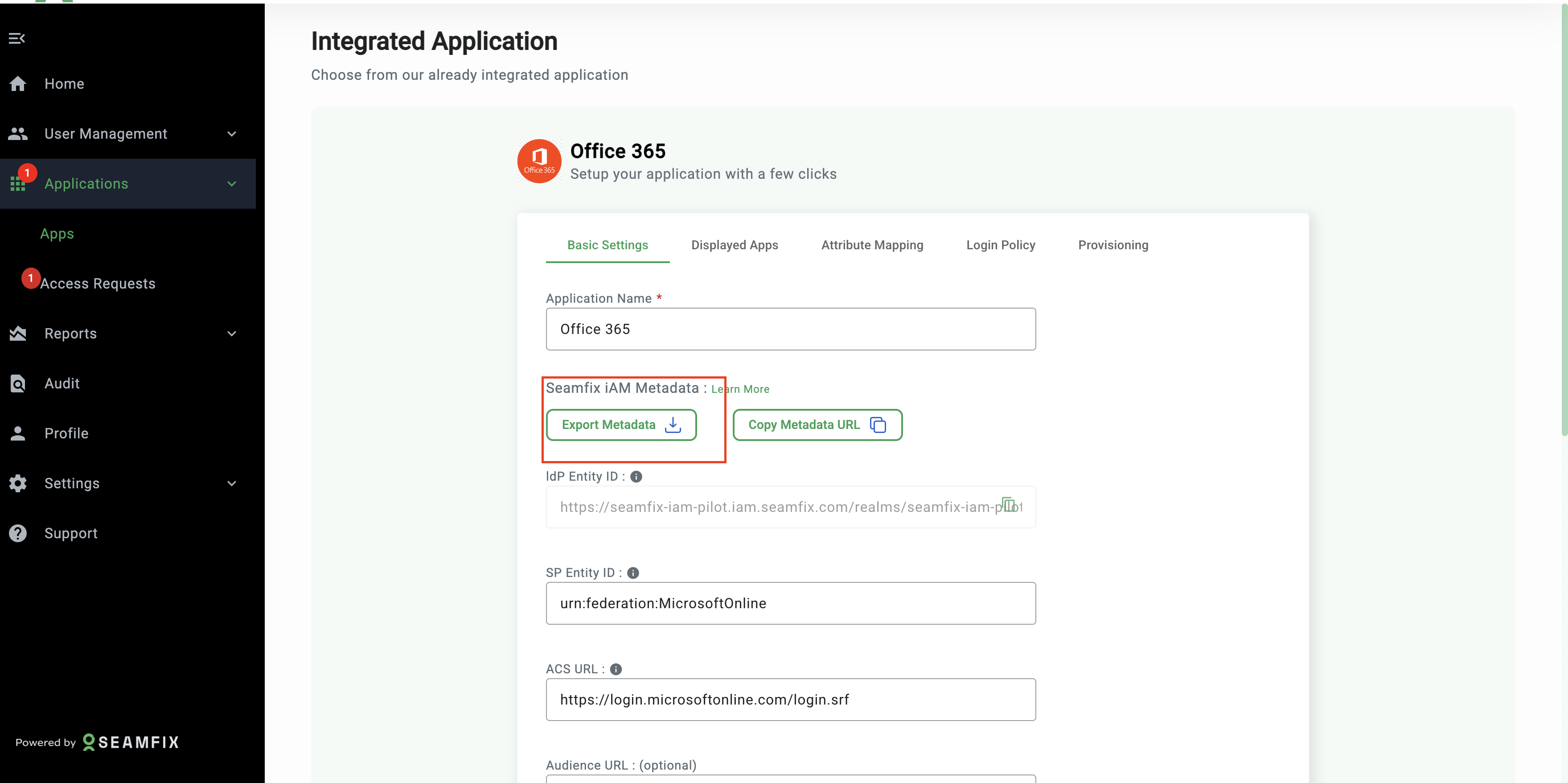
Step 2: Export Metadata and Collect Required Values
On the Office 365 application page in Fixiam:
-
Click Export Metadata
-
This opens an XML file in a new browser tab.
From this file, copy the following values:
-
IdP Entity ID
Find entityID="..." → This this as your IssuerUri that will be used in powershell
-
Single Sign-On URL Find <md:SingleSignOnService Location="..." → Copy the value inside Location=""
This is your PassiveLogOnUri
-
Public Certificate
-
Copy it (as one line) to use as the SigningCertificate in PowerShell
You’ll use all three in PowerShell to configure your federated domain.
Step 3: Set Up Federation in Microsoft 365 (via PowerShell)
Make sure your domain is added and DNS-verified in Azure before proceeding.
a. Connect to Microsoft Online
Connect-MsolService
Log in with your Microsoft 365 global admin credentials.
b. Add the Domain as Federated
Replace yourdomain.com with your actual domain.
New-MsolDomain -Name yourdomain.com -Authentication Federated
c. Retrieve DNS Record and Verify Domain Ownership
Get-MsolDomainVerificationDns -DomainName yourdomain.com -Mode DnsTxtRecord
Add the TXT record to your domain DNS provider.
Once DNS is verified:
d. Confirm and Configure Federation
Prepare values:
$domainname = "yourdomain.com"
$logoffuri = "https://localhost:9900/login/"
$passivelogonuri = "https://localhost:9900/identity/saml"
$issueruri = "https://localhost:9900/identity/saml"
$protocol = "SAMLP"
$cert = "<paste your full certificate here - no spaces or line breaks>"
Then run:
Confirm-MsolDomain -DomainName $domainname -IssuerUri $issueruri `
-FederationBrandName $domainname -LogOffUri $logoffuri `
-PassiveLogOnUri $passivelogonuri -SigningCertificate $cert `
-PreferredAuthenticationProtocol $protocol
Ensure the certificate is pasted as one continuous string.
Step 4: Complete Configuration in Fixiam
Now that the domain is federated:
- Go back to the Office 365 app in IAM
- Fill the following fields using Microsoft details (if not already set) SP Entity ID: our Microsoft Entity ID (from admin portal) ACS URL: Your Microsoft ACS URL (from admin portal) Audience URL(Optional) : Reuse SP Entity ID or leave blank Sign Assertion ✅ Enabled
Attribute Mapping in Fixiam
- Go to Attribute Mapping tab
- Set: Name ID- Email Format-Persistent
Step 5: Set Up Users in Microsoft & Fixiam
a. Create a User in Microsoft:
New-MsolUser -UserPrincipalName [email protected] `
-ImmutableId [email protected] `
-DisplayName "John Doe" -FirstName John -LastName Doe `
-AlternateEmailAddresses "[email protected]"
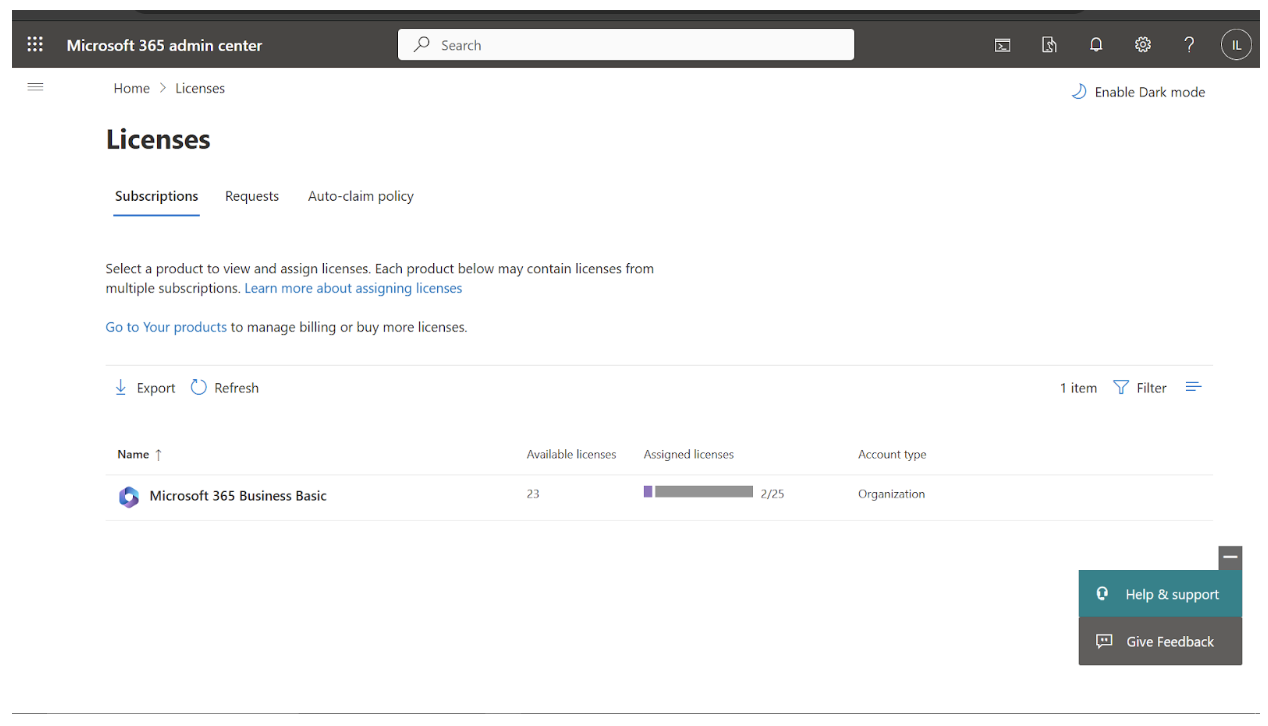
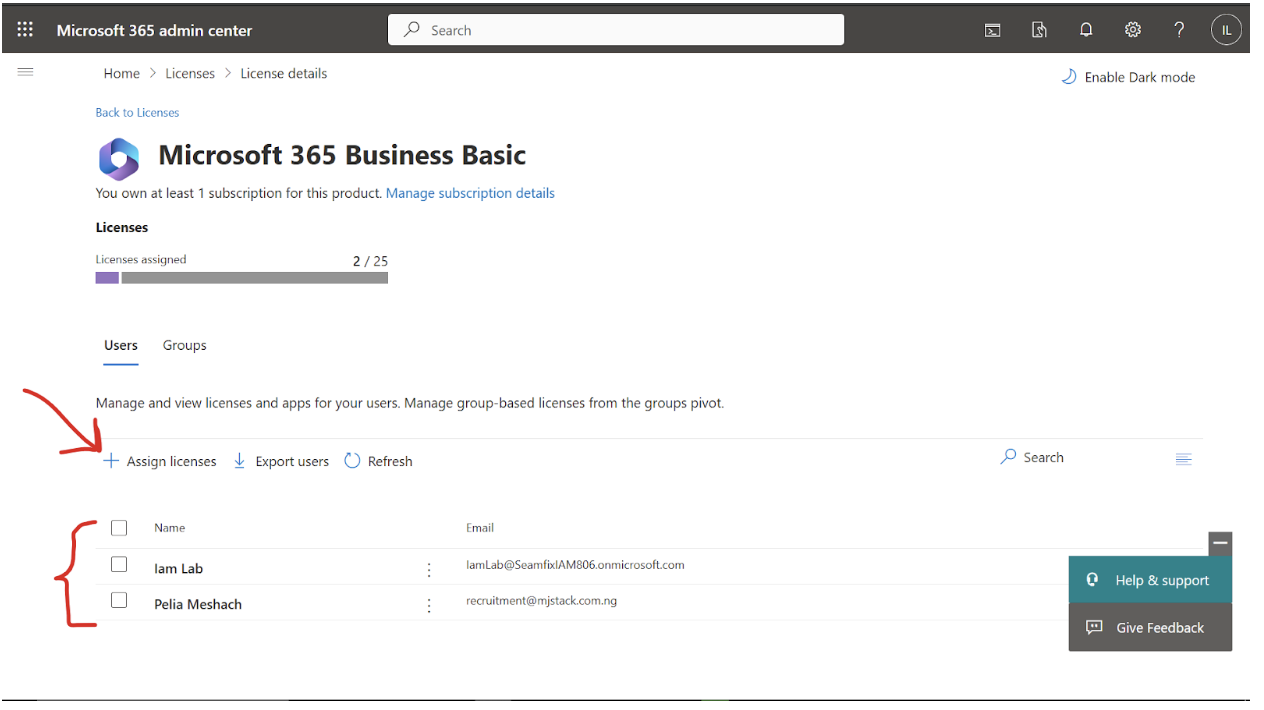
b. Assign License
-
Go to the Microsoft Admin Portal Licenses Page
-
Select a license and assign it to the user
Step 6: Assign IAM App to a Group
- In IAM, go to User Management > Groups
- Create a group (e.g., Office 365 SSO Users)
- Assign the Office 365 app to this group
- Add users with matching emails to the group
Step 7: Test the SSO Integration
- Go to https://portal.office.com
- Enter the test user’s email (e.g., [email protected])
- You should be redirected to Fixiam
- Login with IAM credentials
You’ll be redirected back to Office 365 if successful
Integration Complete!
You've successfully connected Microsoft Office 365 with Fixiam using secure SAML SSO. Users can now sign in once and access their Microsoft tools seamlessly
Updated about 2 months ago
